The execution ledger for every AI action across the enterprise. Every verification, agent decision, and enforcement action is sequenced, cryptographically hashed, and permanently immutable.
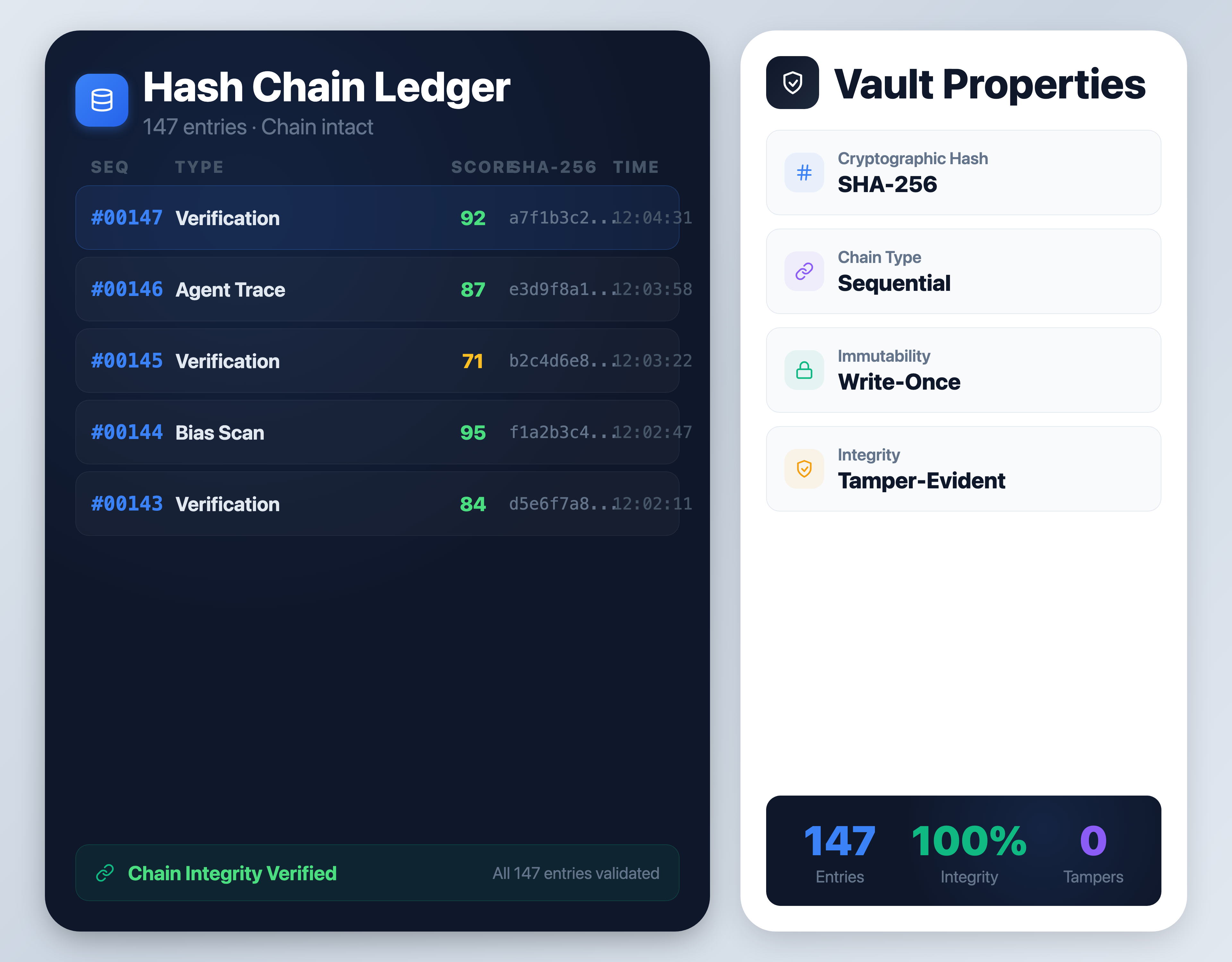
Every verification anchored to an immutable hash chain.
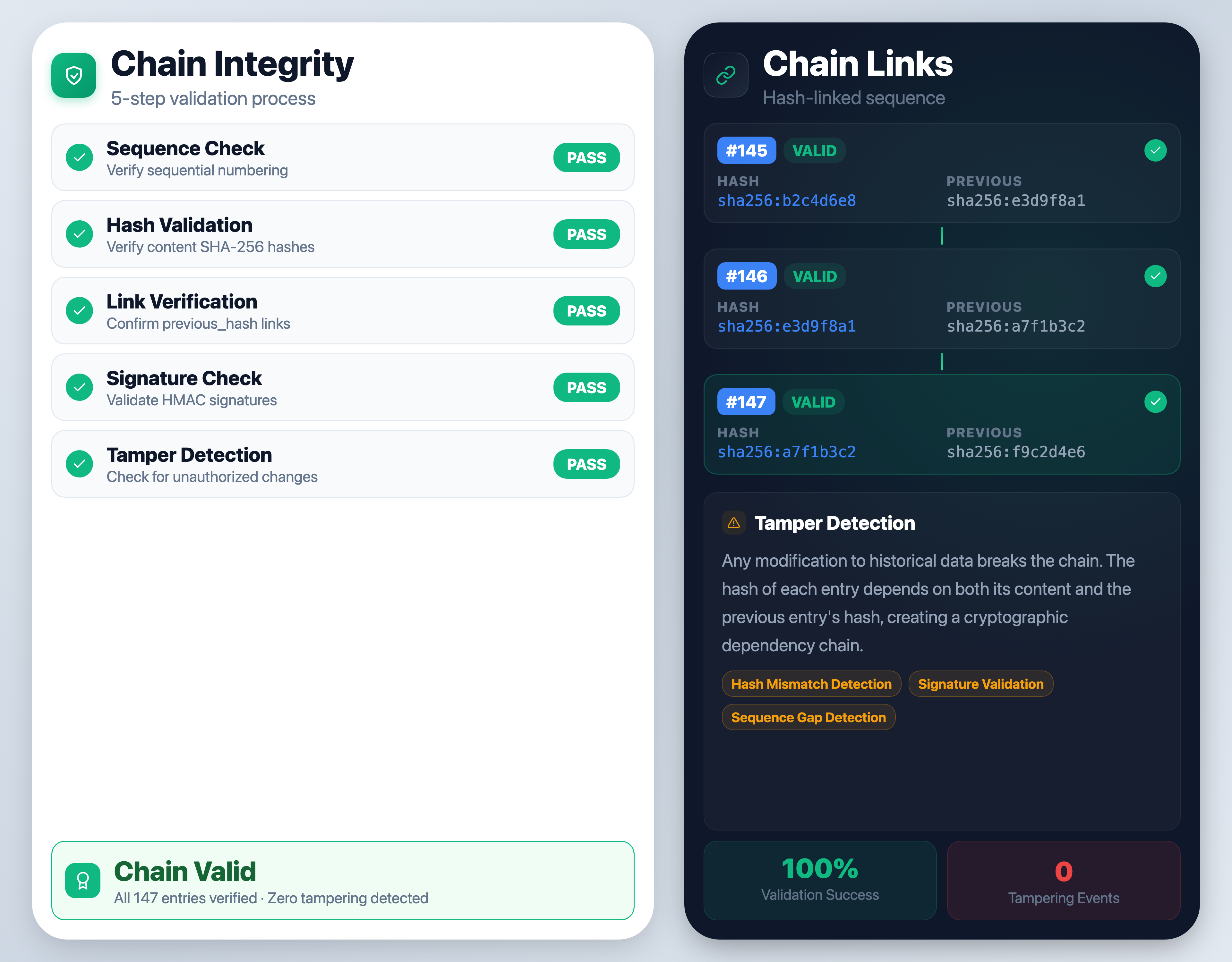
Every entry linked to the previous via SHA-256. Sequence numbers + previous_hash + entry_hash = immutable linked list.
HMAC-SHA256 signature on every entry, verified on every access. Workspace-scoped secrets ensure isolation.
JSON & HTML execution evidence packs with chain validation and integrity certificates. Filter by date range or entry type.
Every API verification automatically creates a signed, chain linked vault entry. No manual steps. No gaps.
/api/v1/verify
finishes with trust score, claims, and governance result.
Content SHA-256 hashed, linked to previous entry's hash, HMAC-signed with workspace secret.
Appended with monotonic sequence number, chain state updated. Entry becomes permanently immutable.
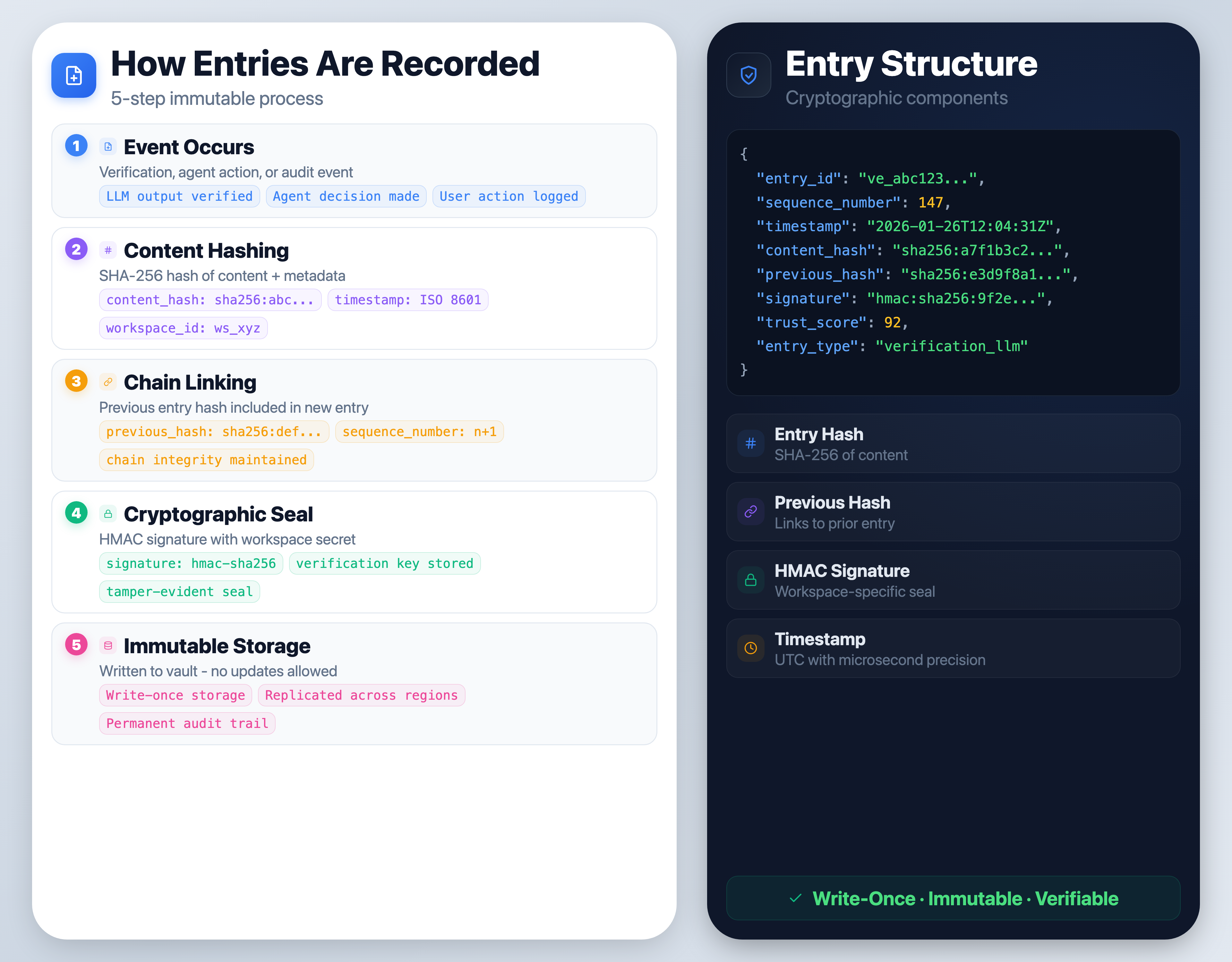
Every AI verification, agent decision, and enforcement action is permanently recorded in the execution ledger. Each record is cryptographically hashed and chained to create a tamper-evident history of how AI systems executed actions across the enterprise.
Model verification events recorded via the API
Multi-step agent execution chains with tool calls
Chain validations, exports, system events
Automatic integrity violation detection
Browse, validate, and export vault entries through the Sentinel Vault v2 API. Every endpoint returns cryptographic proof alongside the data.
{
"entry_id": "ve_a1b2c3d4e5f6...",
"entry_type": "verification_llm",
"sequence_number": 847,
"previous_hash": "e3b0c44298fc...",
"content_hash": "a7f3b9c8d2e1...",
"entry_hash": "9f86d081884c...",
"signature": "d4735e3a265e...",
"trust_score": 82,
"verification_status": "verified",
"verification": {
"signature_valid": true,
"hash_algorithm": "sha256",
"signature_algorithm": "hmac-sha256"
}
}Every entry is cryptographically linked to the one before it. If any entry is modified after the fact, the hash chain breaks immediately.
POST /validate
walks the full chain verifying each hash link, signature, and sequence number.
GET /entries/<id>/proof
returns per-entry cryptographic proofs with chain context.
If any entry is modified, the hash chain breaks immediately. Content hash, entry hash, and HMAC signature all fail together.
Request a demo to see how the Provenance Vault creates an immutable, cryptographically signed audit trail for every AI verification.