Every agent action, authorised in real time. Xybern sits between your agents and the world, enforcing policies before anything runs.
Xybern intercepts every agent action in real time. Each one is evaluated against your policies, logged with a signed decision, and either cleared, blocked, or routed for human review , before the agent touches anything.
Real-time enforcement means nothing runs without a decision. No action slips through unreviewed.
Route sensitive actions to a reviewer instead of a hard block. The agent waits. Work continues.
Every decision is signed and exportable. No manual log assembly when regulators come asking.
Register, monitor, and govern every AI agent from a single place. Know their identity, trust score, assigned policies, and last action at a glance , across every environment you run.
Every agent is registered with a verified identity before it touches production. No action without attribution.
Agent A cannot pass more permissions to Agent B than it holds itself. Enforced at the infrastructure level.
Breakglass gives your team an exit that satisfies your audit trail. No undocumented overrides.
Write, simulate, and deploy enforcement rules as versioned policy objects. Test against real historical traffic before going live. Package into deployable bundles you can roll back in seconds.
Run policy simulation against live traffic to see exactly what a new rule would block before switching it on.
Version control, review, and roll back your enforcement policies the same way your team manages a codebase.
Policy packs ensure your staging and production enforcement stays in sync. No configuration drift.
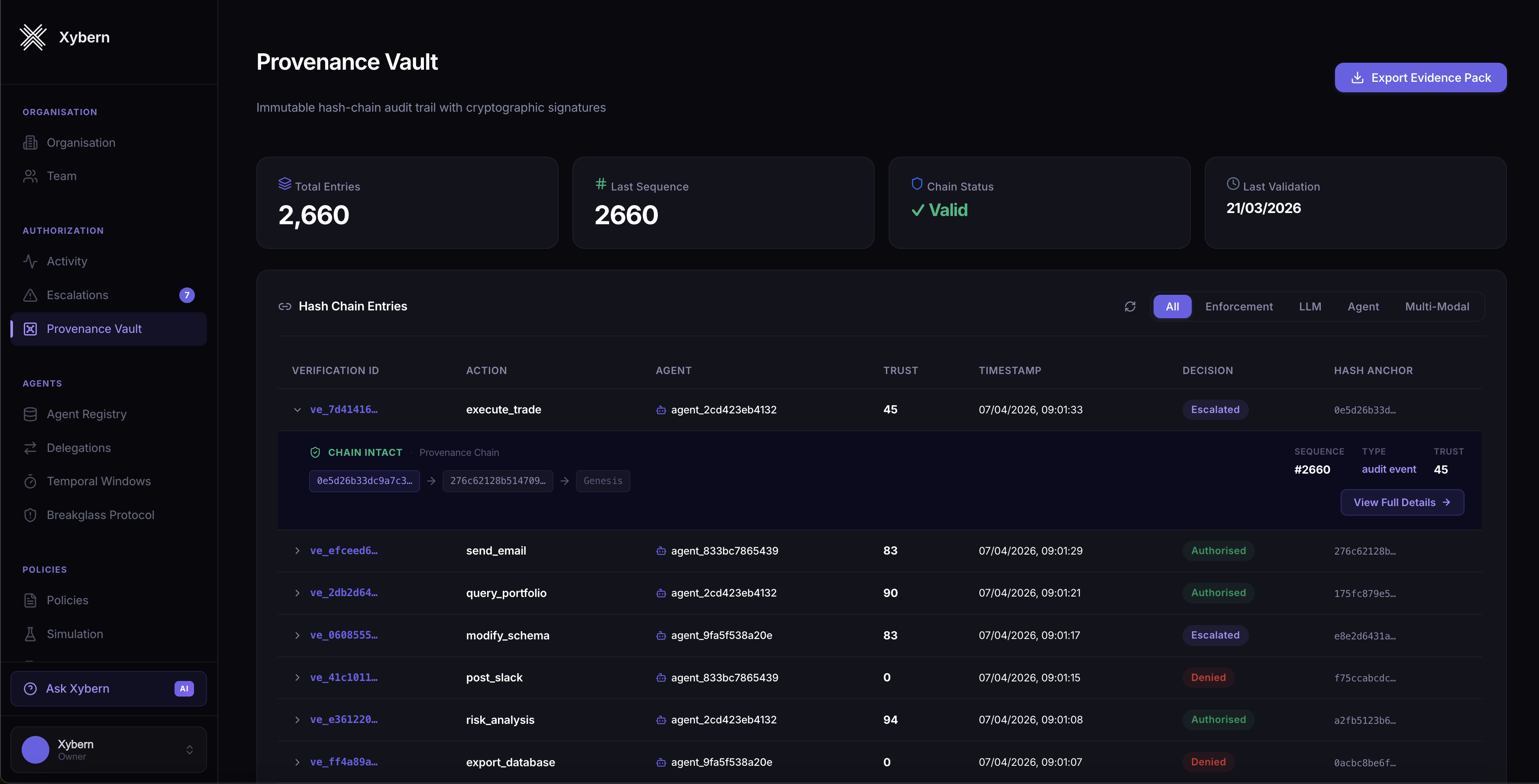
Xybern's Provenance Vault captures a cryptographically signed log of every decision, who authorised it, and why. Designed for regulated industries where auditability is not optional.
Xybern integrates with your existing AI infrastructure without replacing any models or systems. Your engineering team gets full API and SDK access. Your compliance team gets the audit trail.
Xybern is framework-agnostic. Drop it into your existing agent stack with minimal configuration.


Join the teams building enterprise AI with Xybern as their authorisation layer. Request early access today.